Versions Compared
Key
- This line was added.
- This line was removed.
- Formatting was changed.
Access rights
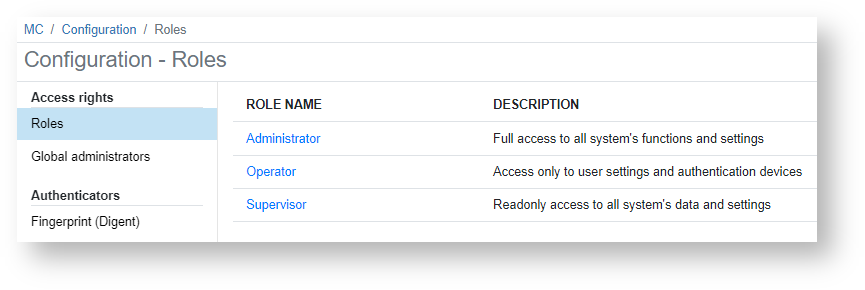
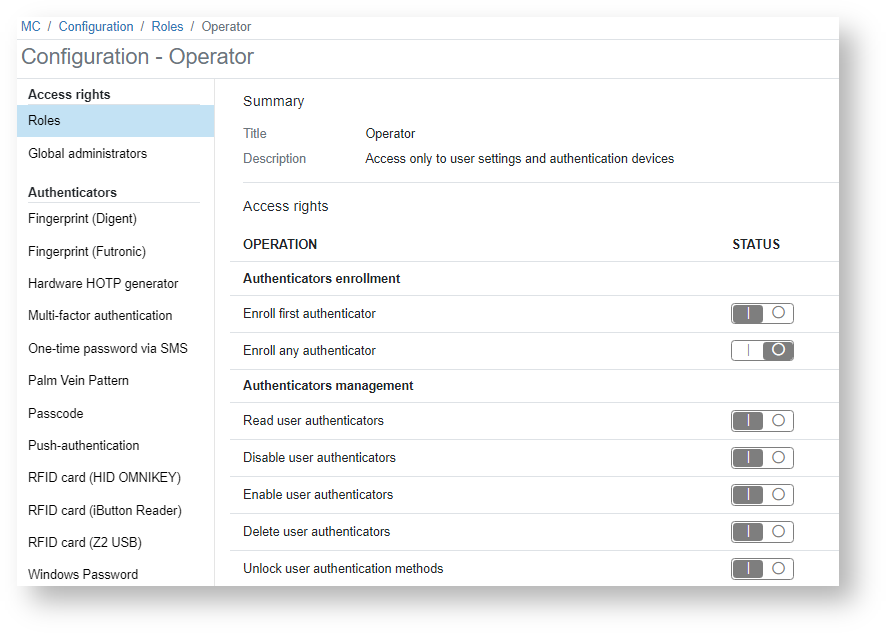
Roles
This section gives an overview of the Indeed PAM system access roles: Administrator, Operator, and Inspector. To get more information about access rights, please click on the appropriate role.
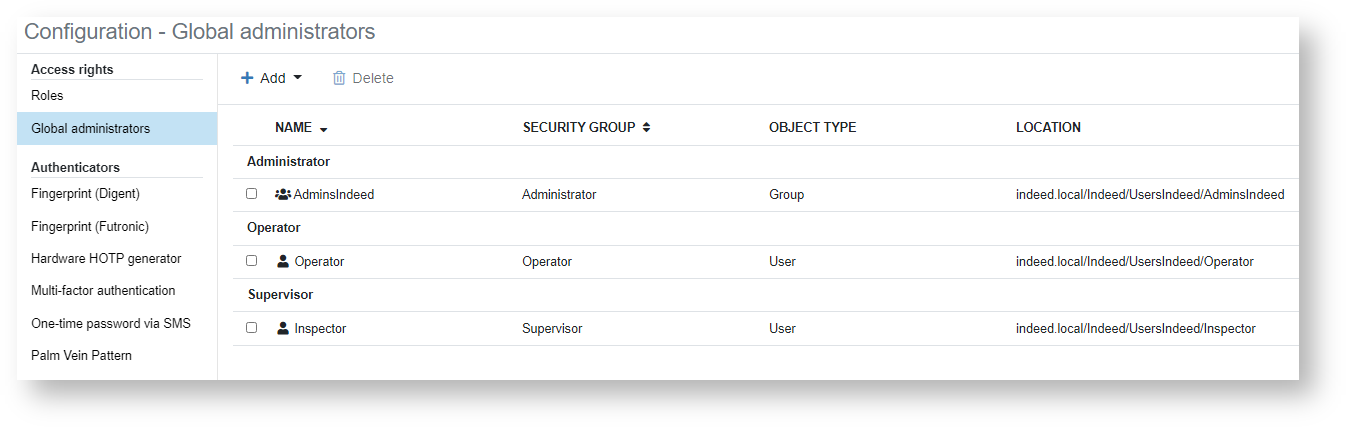
 Global administrators
Global administrators
This section shows the global system administrators for each subgroup. To add an administrator, please follow these steps:
- Click Add and select the appropriate role.
- Select the object type − User or Group.
- Specify the location − an entire user folder or a separate container.
- To run a search, please enter the name or its part in the Name field.
- Click Search.
- Select a user and click on the Add button.
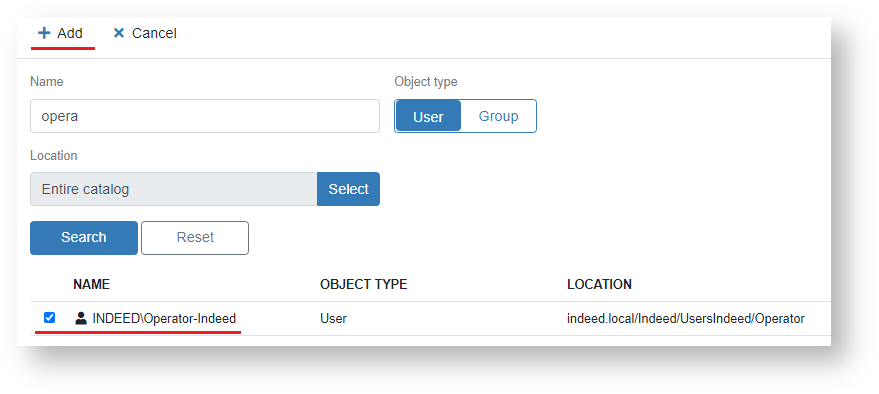
- Once the item has been successfully added, it will be displayed in a corresponding section.
Authenticators
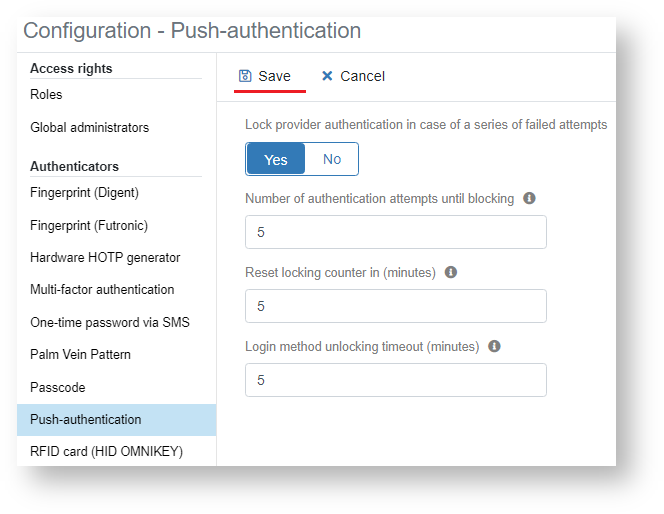
In this section, you can configure settings so that you can automatically lock/unlock authenticators. To do this, please follow these steps:
- Select an authenticator.
- Set the Lock provider authentication in case of a series of failed attemps parameter to Yes.
- Set the permitted number of invalid attempts for the Number of authentication attempts until blocking parameter. Default value: 5
- In the field Reset locking counter in (minutes), set the lockout duration. Default value: 5
- In the field Login method unlocking timeout (minutes), set the timeout duration. Default value: 5
- Click Save.
Access rights table
| Operations | Administrator | Operator | Supervisor |
|---|---|---|---|
Authenticators enrollment | |||
| Enroll first authenticator |  Image Modified Image Modified |
| |
| Enroll any authenticator |
| ||
Authenticators management | |||
| Read user authenticators |
|
|
|
| Disable user authenticators |
|
| |
| Enable user authenticators |
|
| |
| Delete user authenticators |
|
| |
| Unlock user authentication methods |
|
| |
| Get user authentication method |
|
|
|
| Enable user authentication methods |
|
| |
| Disable user authentication methods |
|
| |
| Get user authentication method state |
|
|
|
| Set auth method settings |
| ||
| Get auth method settings |
|
| |
| Set user auth method settings |
|
| |
| Get user auth method settings |
|
|
|
| Set module auth method settings |
|
| |
| Get module auth method settings |
|
|
|
| Set authenticator rights |
|
| |
| Get authenticator rights |
|
|
|
| Set auth method settings for policy |
|
| |
| Get auth method settings for policy |
|
|
|
License management | |||
| Register licenses |
| ||
| Unregister licenses |
| ||
| Enumerate registered licenses |
|
|
|
| Acquire user licenses |
|
| |
| Release user licenses |
|
| |
| Enumerate user licenses |
|
|
|
Access control management | |||
| Add catalog object to access group |
| ||
| Remove catalog object from access group |
| ||
| Enumerate access group members |
|
|
|
Hardware devices management | |||
| Create hardware device |
| ||
| Update hardware device |
| ||
| Enumerate hardware devices |
|
|
|
| Remove hardware device |
| ||
Policies management | |||
| Create policy |
| ||
| Update policy |
| ||
| Remove policy |
| ||
| Get policies |
|
|
|
| Get policy users |
|
|
|
| Set policy users |
|
| |
| Get policy applications |
|
|
|
| Set policy applications |
| ||
| Get policy priority |
|
|
|
| Set policy priority |
| ||
User cache management | |||
| Enable cache |
|
| |
| Disable cache |
|
| |
| Check cache enabled |
|
| |
| Set cache settings |
| ||
| Get cache settings |
|
|
|
User accounts management | |||
| Create account |
| ||
| Remove account |
| ||
| Get account |
|
|
|
| Get account state |
|
|
|
| Set password |
| ||
| Check for password is set |
|
| |
| Set login |
|
| |
| Get login |
|
|
|
| Set account settings |
|
| |
| Get account settings |
|
|
|
| Set custom fields |
|
| |
| Get custom fields |
|
|
|
| Change password random |
| ||
| Change password |
| ||
Business applications management | |||
| Get applications |
|
|
|
| Create application |
| ||
| Set application |
|
| |
| Remove application |
| ||
Backtotop
| Table of Contents | ||
|---|---|---|
|